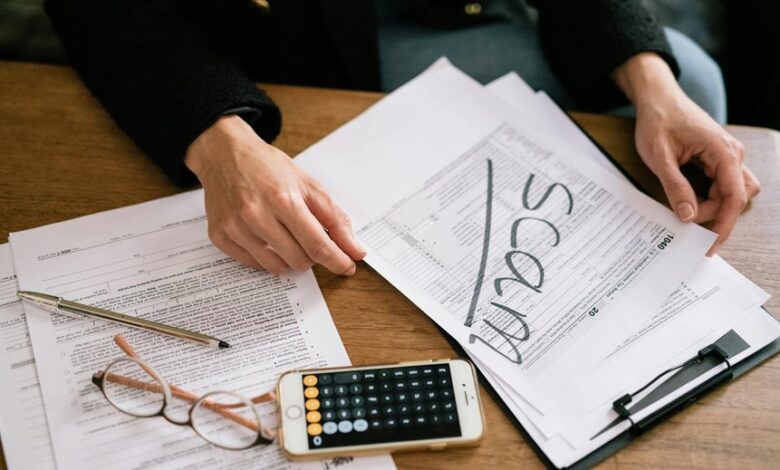
Scam Investigation Research Portal Phone Number Scam Lookup Explaining Fraud Search Methods
A scam investigation portal for phone number fraud lookup standardizes how data is gathered and analyzed across multiple sources. It presents a transparent workflow that aggregates call records, carrier flags, geolocation, and social signals to map risk profiles. Credible sources, verification steps, and reproducible procedures are emphasized to support objective assessments. The approach aims for rigorous documentation and neutrality, guiding researchers toward actionable insights while inviting further scrutiny to confirm patterns and implications. Yet questions remain about scalability and verification gaps that require ongoing attention.
What Is a Scam Investigation Portal and Why It Matters
A scam investigation portal is a centralized platform designed to collect, analyze, and disseminate information about suspected fraudulent activities and related phone-number scams. It functions as a repository and coordination hub for investigators and researchers.
The portal supports scam investigations and fraud research by standardizing reporting, enabling cross-references, and fostering transparency while preserving analytic objectivity and user autonomy.
How Phone Number Lookups Work in Fraud Research
Phone number lookups in fraud research assemble data from multiple sources to identify patterns tied to suspicious activity. In practice, analysts aggregate call records, carrier flags, geolocation, and social signals to map risk profiles. The process emphasizes fraud research rigor, careful handling of phone lookups, and vigilance for authenticity risk, preserving data integrity while enabling informed decisions about potential threats.
Evaluating Sources: Credibility, Red Flags, and Verification Steps
Evaluating sources in fraud research requires a systematic approach to determine credibility, identify red flags, and implement verification steps. The analysis remains detached, focusing on evidence quality, methodological soundness, and source provenance. Criteria include corroboration, transparency, and tone neutrality. Evaluating sources emphasizes process over rumor, highlighting credibility red flags such as anonymous authorship, unverifiable data, and biased framing. Verification steps ensure reproducibility and defend against manipulation.
Practical Workflow: From Discovery to Verification and Action
Indeed, a structured workflow guides fraud researchers from initial discovery through verification and decisive action, ensuring that each step builds on verifiable evidence and traceable procedures.
The practical workflow emphasizes disciplined data collection, cross-checking sources, and documenting decisions.
Verification steps correlate findings with corroborating records, enabling objective judgments while preserving autonomy, transparency, and accountability in the investigative process.
Conclusion
The assessment underscores a disciplined, reproducible framework for scam investigations, where diverse data streams are integrated to form credible risk profiles. By prioritizing source credibility, verification, and transparent decision logs, researchers can map patterns with objectivity and accountability. The approach minimizes bias and enhances replicability, enabling proactive prevention and informed action. In short, integrity and methodical rigor keep investigations on solid footing, avoiding snap judgments and ensuring findings endure scrutiny, even under pressure.




