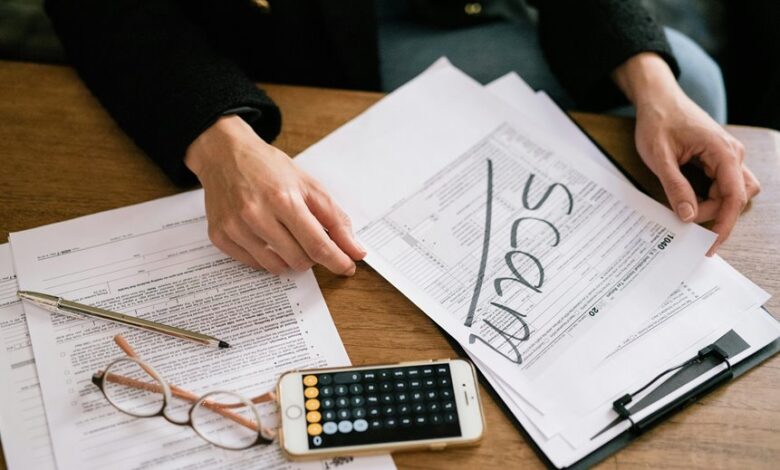
Fraud Caller Investigation Portal Phone Scam Lookup Revealing Scam Phone Search Queries
The Fraud Caller Investigation Portal leverages phone scam lookup to surface search queries tied to suspicious calls. Analysts examine spoofing cues, pretext narratives, and timing signals to distill actionable patterns. The system highlights targeted phrases and tactics, revealing evolving schemes while preserving privacy and verification standards. This approach yields concrete indicators for defense, yet leaves open questions about context and limits, inviting further scrutiny and ongoing assessment of threat intelligence.
What the Fraud Caller Investigation Portal Reveals About Scam Signals
The Fraud Caller Investigation Portal systematically aggregates indicators associated with scam calls, enabling analysts to distill patterns from disparate data sources. It identifies fraud indicators, maps caller patterns, and quantifies risk, while upholding data privacy standards. Findings inform security training and policy—empowering informed, independent action. The approach remains analytical, decisive, and rigorous, ensuring transparent insights without compromising operational freedom.
How Lookup Queries Expose Spoofing and Pretexting Tactics
Lookup queries act as a diagnostic lens, revealing how spoofing and pretexting unfold in real time by exposing the underlying cues callers use to mask identity and intent. The analysis centers on examining spoofing patterns and identifying pretexting motives, delineating how misleading narratives align with technical indicators. This precise scrutiny informs adaptive defenses, empowering users to recognize deception and pursue transparent verification.
Reading the Red Flags: Common Phrases and Caller Behavior to Watch For
Reading the red flags begins with a systematic inventory of phrases and behaviors that commonly accompany fraudulent calls. The analysis notes red flags in interchangeable timing, pressure, and vague authority. Typical caller behavior shifts from urgency to evasiveness, while scam signals include mismatch details and insistence on rapid action. Awareness counters spoofing tactics and reinforces disciplined, preventative decision-making for freedom-minded readers.
Turning Data Into Defense: Verifying Suspicious Calls and Staying Safe
Turning data into defense requires a disciplined approach to verifying suspicious calls and maintaining user safety. The analysis concentrates on corroborating sources, cross-checking numbers, and isolating anomalies before alerting users. It emphasizes data privacy and ethical handling of evidence, recognizing scam psychology patterns without sensationalism. Decisions rely on repeatable processes, transparency, and proactive warnings to preserve autonomy and reduce exposure to fraud.
Conclusion
In meticulous analysis, the Fraud Caller Investigation Portal acts as a forensic lamp, revealing hidden fingerprints of deception within scam calls. By mapping spoofing cues, pretexts, and timing, it converts chaotic chatter into actionable patterns, reducing ambiguity to a crisp diagnostic signal. The system’s privacy-preserving safeguards ensure illumination without overreach, guiding analysts toward decisive verifications. Ultimately, data becomes defense: a disciplined, transparent shield that narrows risk, enabling proactive defenses while preserving operational integrity.




